Overview
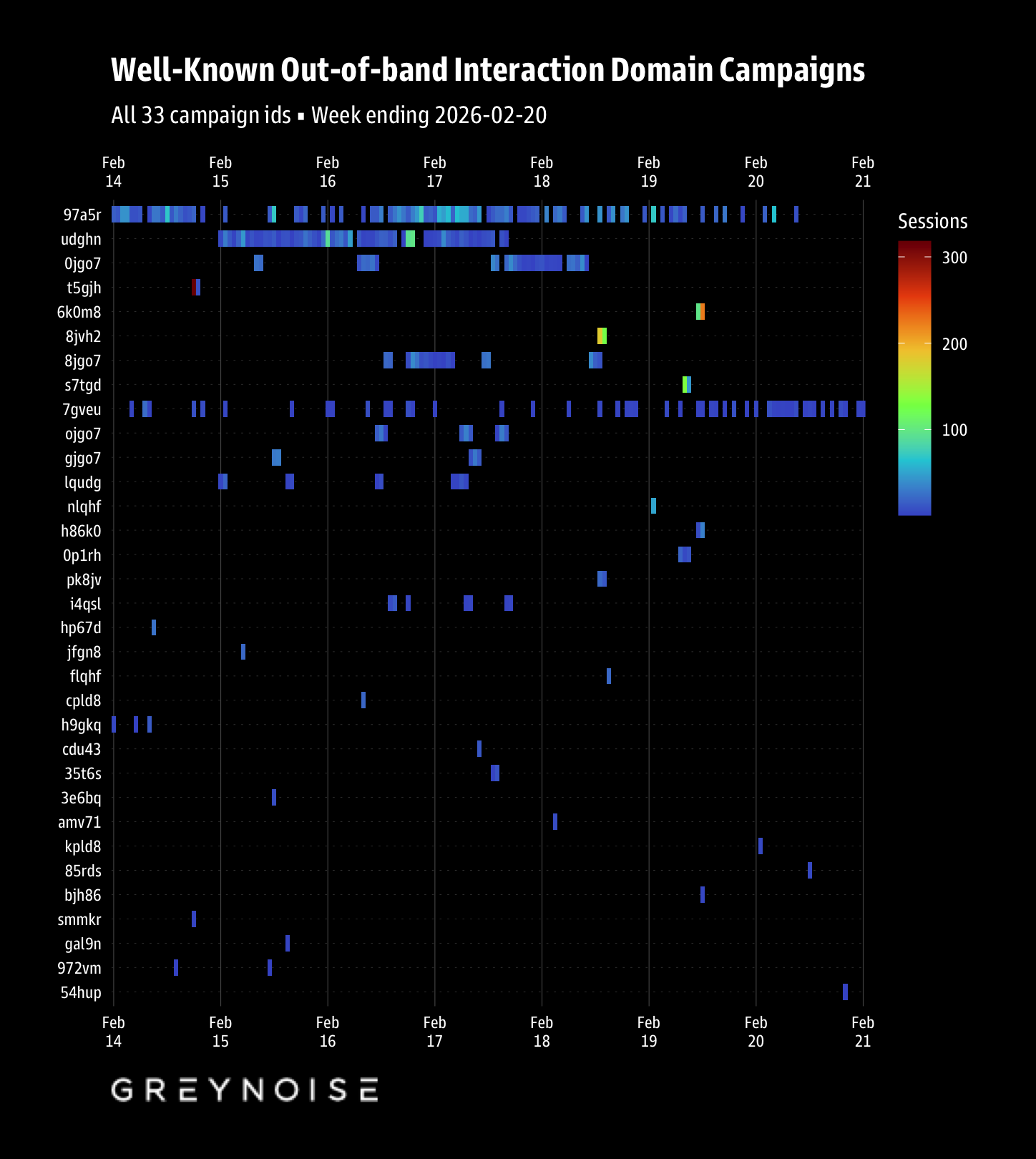
Between February 14 and February 20, 2026, GreyNoise sensors recorded 5,695 OAST domain occurrences across 3,882 distinct sessions originating from 24 unique source IPs. All 5,695 rows decoded successfully (100% decode rate) using the Interactsh encoding scheme, yielding 33 distinct campaign identifiers and 5,560 unique callback domains.
OAST domains appeared across multiple HTTP fields: request bodies (1,724 occurrences, 30.3%), request header values (1,389, 24.4%), request cookies (1,284, 22.5%), URI paths (1,063, 18.7%), user-agent strings (149, 2.6%), and URL paths (86, 1.5%). Compared to the previous week, cookie-based injection increased from 4.7% to 22.5%, indicating a shift in scanning toolkit configurations toward cookie-based payload delivery.
JA4T TCP fingerprint analysis from session data identified 12 unique fingerprints. The Nuclei/loopback cluster (MSS 65495) remains dominant at 2,547 sessions across 15 IPs. Standard Linux signatures (MSS 1460) accounted for 669 sessions. Two anomalous fingerprints provide high-confidence actor tracking: window size 32120 (Private Layer custom stack) and TCP options 2-1-1-4-1-3 (AnchorFree VPN node).
Seven multi-fingerprint IPs indicate dual-tool deployment. The most notable is 80.87.206.76 (OVH/Alliance LLC Moscow) with 941 sessions split across two Nuclei variants (65495 window: 913 sessions; 33280 window: 28 sessions).
Temporal Analysis
Activity distributed evenly across the week with a partial day on February 20:
| Day | OAST Count | Sessions | Unique IPs |
|---|---|---|---|
| Feb 14 | 722 | 512 | 7 |
| Feb 15 | 707 | 512 | 8 |
| Feb 16 | 1,215 | 714 | 9 |
| Feb 17 | 1,176 | 790 | 11 |
| Feb 18 | 892 | 665 | 11 |
| Feb 19 | 840 | 612 | 8 |
| Feb 20 | 143 | 77 | 5 |
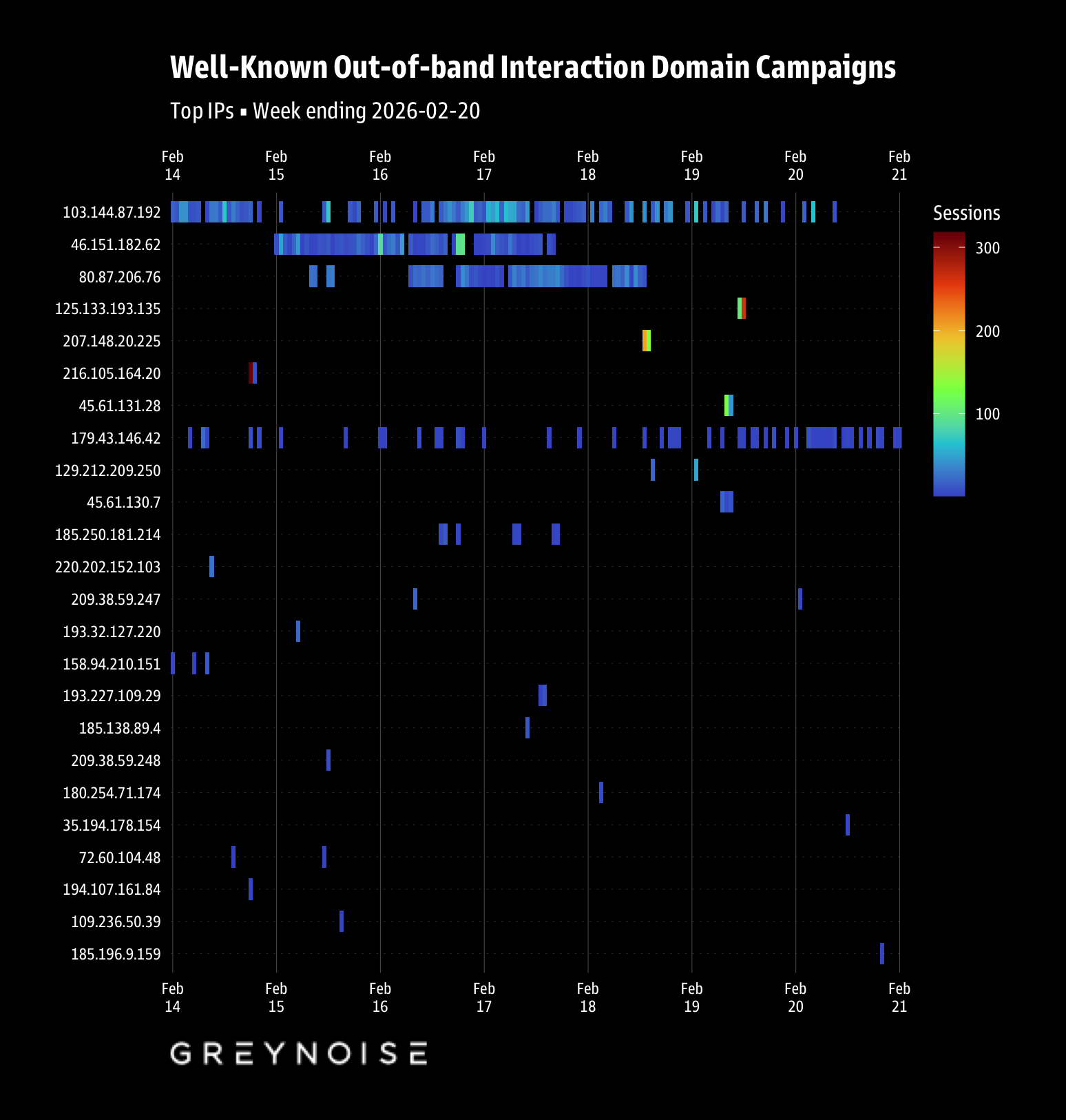
February 16-17 saw peak activity coinciding with weekend scanning operations. Burst analysis identified concentrated activity at Feb 19 11:00 UTC (336 sessions from only 2 IPs – Ghosty Networks and Viet Storage), Feb 14 18:00 UTC (305 sessions, 3 IPs), and Feb 18 13:00 UTC (255 sessions, 4 IPs).
The February 20 drop-off reflects incomplete data collection for the final day of the observation window.
Campaign Analysis
All 33 campaigns map to single-IP operations. Six IPs appear across multiple campaigns, indicating sequential tool runs from the same infrastructure.
Campaign Group 1: Viet Storage High-Volume Scanner
IP: 103.144.87.192 (AS135932, Viet Storage, Vietnam)
Sessions: 741 | Campaigns: 1 (97a5r) | OAST Domains: 2,138
The highest-volume single-IP operation this week, generating 2,138 OAST domains across 741 sessions. Campaign 97a5r also appeared in the previous week’s data (Feb 9-13), indicating sustained operation spanning both observation windows. GreyNoise has tracked this IP since 2025-10-14 with 707,471 total hits across 1,183 sensors. Dual JA4T fingerprints: 65495 (562 sessions) and 33280 (179 sessions), both with MSS 65495 confirming Nuclei deployment. The domain-to-session ratio of 2.88 (2,138/741) indicates multi-vector payload injection per session.
Campaign Group 2: Ghosty Networks / DEMENIN B.V.
IP: 46.151.182.62 (AS205759, Ghosty Networks LLC, Luxembourg)
Sessions: 699 (udghn: 615, lqudg: 84) | OAST Domains: 921
Brand new infrastructure: GreyNoise first observed this IP on 2026-02-13, only one day before our observation window. Despite its recent appearance, it accumulated 98,647 GreyNoise hits but targets only 1 sensor, suggesting focused targeting. VirusTotal classifies it at 11.8% malicious (11/93 engines) – the highest detection rate among all IPs this week. Censys reveals Ubuntu with OpenSSH 8.9p1, SSH (22), and a Valve/Source Engine gaming protocol on UDP 27015. The gaming server protocol is unusual for a scanning host and may indicate compromised infrastructure. Dual JA4T fingerprints confirm Nuclei deployment.
Campaign Group 3: OVH / Alliance LLC Moscow
IP: 80.87.206.76 (AS16276, OVH SAS, France)
Sessions: 941 | Campaigns: 4 (0jgo7, 8jgo7, gjgo7, ojgo7) | OAST Domains: 418
The four campaigns share a *jgo7 naming pattern, indicating sequential automated tool runs. This is the longest-established scanner observed: GreyNoise first seen 2023-03-23, with 184,902 total hits across 2,599 sensors. Censys WHOIS reveals the actual registrant as Alliance LLC, Moscow, Russia, operating through French OVH hosting. Forward DNS resolves to the suspicious domain ir6k1.2monkeyd.online. Gmail-based abuse contact (nocalliance64@gmail.com) instead of corporate email indicates intentional anonymization. ProxyLogon SSRF (CVE-2021-26855) was the primary exploitation focus with 564 sessions. Dual Nuclei JA4T fingerprints with 913/28 session split.
Campaign Group 4: Korea Telecom Burst Scanner
IP: 125.133.193.135 (AS4766, Korea Telecom, South Korea)
Sessions: 333 | Campaigns: 3 (6k0m8, bjh86, h86k0)
An ISP IP running a Proxmox VE virtualization host (confirmed by VirusTotal SSL certificate for misspelled “promox.d”). Censys JA4T shows non-standard TCP option ordering (2-1-3-4-8), matching the VPN/tunnel artifact pattern. JA4T 64240_2-4-8-1-3_1460_10 with TTL 10 is distinctive. GreyNoise tags include CVE-2026-1731 (BeyondTrust) and CVE-2026-23760 (SmarterMail), both 2026 critical RCE vulnerabilities.
Campaign Group 5: Vultr Single-IP Scanner
IP: 207.148.20.225 (AS20473, Vultr, United States)
Sessions: 317 | Campaigns: 2 (8jvh2, pk8jv)
Long-established scanner (GreyNoise first seen 2019-05-25), JA4T 42340_2-4-8-1-3_1460_10 shares the unusual TTL 10 with Korea Telecom IP but different window size. Both campaigns ran Feb 14-18.
Campaign Group 6: AnchorFree/Hotspot Shield VPN Exit
IP: 216.105.164.20 (AS9009, M247, United States)
Sessions: 293 | Campaign: 1 (68ieo)
Censys confirms this is a commercial Hotspot Shield VPN exit node operated by AnchorFree (now Aura). Certificate chain uses “Hydra Authentication RSA SubCA #146” (AnchorFree’s proprietary VPN protocol, not malware). The node runs IPSec (IKE), OpenVPN, and Hydra VPN simultaneously, with HashiCorp Consul cluster membership on port 8301. JA4T 42340_2-1-1-4-1-3_1460_7 with non-standard TCP option ordering (2-1-1-4-1-3) is the AnchorFree VPN stack signature. GreyNoise shows first/last seen both 2026-02-14 – a single-day burst through this VPN exit. The actual scanner is behind the VPN.
Campaign Group 7: RouterHosting/Cloudzy Mass Scanner
IP: 45.61.131.28 (AS14956, RouterHosting LLC, United States)
Sessions: 350 | Campaigns: 2 (bpm5j, kpm5j)
Brand new infrastructure (GreyNoise first seen 2026-02-19, 2 days before observation) with 983,466 hits across 4 sensors – extremely high volume for a fresh IP. Censys labels this BULLETPROOF (0.75 confidence). Zero exposed services despite massive scanning volume, indicating purpose-built scanner with no inbound access. VirusTotal WHOIS reveals FranTech Solutions (PONYNET) as the parent company, with abuse contact at cloudzy.com – a documented bulletproof hosting reseller used by ransomware operators and APTs. JA4T 64240_2-4-8-1-3_1460_7 (standard Linux). Operated only Feb 19-20.
Campaign Group 8: Private Layer / Switzerland (Continuing)
IP: 179.43.146.42 (AS51852, Private Layer INC, Switzerland)
Sessions: 175 | Campaigns: 3 (7gveu, lgveu, 8gveu)
Continues from last week’s report. Censys confirms BULLETPROOF hosting (0.75 confidence). Three exposed services: SSH (22), HTTP auth-protected (8082), and nginx default page (8084). Port 8089 (previously “Restricted”) is no longer visible, suggesting infrastructure rotation. VirusTotal shows the aliyundunupdate.xyz typosquat domain still resolving to this IP, with a new URL http://179.43.146.42/x (Feb 19) suggesting active C2 payload hosting. The unique TCP window size 32120 appears in 101 sessions and serves as a high-confidence single-actor tracking identifier. GreyNoise now tags this IP with both CVE-2026-0770 (Langflow RCE, new this week) and CVE-2026-1731 (BeyondTrust), indicating an expanding exploitation toolkit.
Remaining Campaigns
| IP | ASN | Sessions | Campaigns | JA4T | Notes |
|---|---|---|---|---|---|
| 185.138.89.4 | AS215540 | 12 | 1 (ka1vu) | 64240_2-1-3-1-1-4_1360_8 |
Replaces 46.29.235.157 from last week in same ASN; MSS 1360 = tunnel |
| 185.250.181.214 | AS49232 | 33 | 1 (n4d7k) | 64240_2-4-8-1-3_1460_7 |
Standard Linux, NL |
| 193.227.109.29 | AS48090 | 7 | 1 (e8kq8) | 64240_2-4-8-1-3_1460_7 |
Standard Linux, DE |
| 193.32.127.220 | AS39351 | 21 | 1 (asnfa) | Mixed (see below) | Sweden, unusual JA4T |
| 194.107.161.84 | AS204009 | 2 | 1 (8ik42) | 65535_2-4-8-1-3_1460_9 |
TTL 9, FR |
| 209.38.59.247 | AS14061 | 14 | 1 (dg0rn) | 65495_2-4-8-1-3_65495_7 |
DigitalOcean Nuclei |
| 209.38.59.248 | AS14061 | 7 | 1 (1g0rn) | 65495_2-4-8-1-3_65495_7 |
DigitalOcean Nuclei pair |
| 129.212.209.250 | AS31898 | 28 | 1 (t83rm) | 65495_2-4-8-1-3_65495_7 |
Oracle Cloud Nuclei |
| 35.194.178.154 | AS15169 | 5 | 1 (r9qd8) | 65320_2-4-8-1-3_1420_7 |
Google Cloud, MSS 1420 |
| 45.61.130.7 | AS14956 | 34 | 1 (pm5jt) | 64240_2-4-8-1-3_1460_7 |
RouterHosting, same /22 as 45.61.131.28 |
| 158.94.210.151 | AS47583 | 7 | 1 (pqk6r) | 65495_2-4-8-1-3_65495_7 |
Hostinger Nuclei |
| 185.196.9.159 | AS44477 | 1 | 1 (05jjc) | 64240_2-4-8-1-3_1400_7 |
MSS 1400 (tunnel), NL |
| 220.202.152.103 | AS4837 | 4 | 1 (nq8bk) | Mixed | China Unicom, only non-noise IP per GreyNoise |
Notable: 193.32.127.220 (31173 Services AB, Sweden) uses JA4T 65535_2-1-3-1-1-8-4-0_1284_6 – a highly anomalous fingerprint with MSS 1284 (low, multi-hop tunnel), TTL 6 (proxy chain), and uncommon TCP option ordering including option 8 and 0. This fingerprint has not been observed in previous weeks.
Payload Analysis
Tag-based CVE classification from Arkime session metadata:
| Payload Type | Occurrences | Unique IPs | Campaigns | Notes |
|---|---|---|---|---|
| Log4j RCE (CVE-2021-44228) | 1,997 | 10 | 12 | Continues to dominate OAST volume |
| ProxyLogon SSRF (CVE-2021-26855) | 950 | 5 | 6 | OVH/Alliance LLC primary user |
| Generic Suspicious Linux Command | 771 | 13 | 15 | Cross-cutting indicator |
| Fastjson RCE | 173 | 8 | 10 | Java deserialization |
| SysAid XXE (CVE-2025-2775/2776/2777) | ~50 | 3 | 4 | 2025 CVEs |
| Grafana XSS (CVE-2025-4123) | ~20 | 2 | 2 | 2025 CVE |
| Oracle E-Business (CVE-2025-61882) | ~10 | 2 | 2 | 2025 CVE |
| Ivanti EPMM (CVE-2026-1281) | 2 | 1 | 1 | 2026 CVE, Korea Telecom IP |
| MCP and SSE Endpoint Scanning | 7 | 3 | 3 | New: AI/LLM infrastructure targeting |
The “MCP and SSE endpoint scanning” tag (7 occurrences, 3 IPs) is a new development, reflecting attacker interest in AI/LLM infrastructure exposed via Model Context Protocol and Server-Sent Events endpoints.
Log4j continues to account for the plurality of OAST callbacks despite being over 4 years old. The persistence of Log4j scanning suggests either (a) continued discovery of unpatched instances or (b) Log4j payloads serving as baseline capability tests in automated scanning toolkits.
Infrastructure Analysis
JA4T Fingerprint Clusters
|————-|——–|————“|—–|—-:|———”|—-“|————-| | 65495_2-4-8-1-3_65495_7 | 65495 | Standard | 65495 | 7 | 2,223 | 12 | Nuclei/loopback primary | | 64240_2-4-8-1-3_1460_10 | 64240 | Standard | 1460 | 10 | 333 | 1 | Korea Telecom, unusual TTL | | 33280_2-4-8-1-3_65495_7 | 33280 | Standard | 65495 | 7 | 324 | 3 | Nuclei variant | | 42340_2-4-8-1-3_1460_10 | 42340 | Standard | 1460 | 10 | 317 | 1 | Vultr, TTL 10 match | | 42340_2-1-1-4-1-3_1460_7 | 42340 | Non-standard | 1460 | 7 | 293 | 1 | AnchorFree VPN stack | | 64240_2-4-8-1-3_1460_7 | 64240 | Standard | 1460 | 7 | 252 | 5 | Standard Linux | | 32120_2-4-8-1-3_1460_7 | 32120 | Standard | 1460 | 7 | 102 | 2 | Private Layer unique | | 64240_2-1-3-1-1-4_1360_8 | 64240 | Non-standard | 1360 | 8 | 15 | 2 | AS215540 tunnel | | 65535_2-1-3-1-1-8-4-0_1284_6 | 65535 | Non-standard | 1284 | 6 | 15 | 1 | Deep proxy chain | | 65320_2-4-8-1-3_1420_7 | 65320 | Standard | 1420 | 7 | 5 | 1 | Google Cloud |
Nuclei/loopback cluster (MSS 65495): 2,547 sessions, 15 IPs. This remains the dominant fingerprint group, accounting for 65.6% of all sessions. The MSS 65495 value is a Linux loopback interface artifact, confirming that scanning tools run locally and route OAST callbacks through the loopback adapter.
Non-standard TCP options cluster: Three distinct non-standard option orderings observed: - 2-1-1-4-1-3 (AnchorFree VPN): 293 sessions, confirmed commercial VPN infrastructure - 2-1-3-1-1-4 (AS215540 tunnel): 15 sessions, MSS 1360 confirms encapsulation overhead - 2-1-3-1-1-8-4-0 (deep proxy chain): 15 sessions, MSS 1284 and TTL 6 indicate multi-hop traversal
TTL anomalies: Two IPs share TTL 10 (Korea Telecom and Vultr) despite different window sizes. Standard internet paths produce TTLs of 50-128. TTL 10 suggests either a very close network hop or deliberate TTL manipulation.
Multi-Fingerprint IPs (Dual-Tool Deployment)
| IP | ASN | Fingerprints | Sessions | Interpretation |
|---|---|---|---|---|
| 80.87.206.76 | OVH | 65495/33280 (both MSS 65495) | 941 | Two Nuclei window variants |
| 46.151.182.62 | Ghosty | 65495/33280 (both MSS 65495) | 746 | Two Nuclei window variants |
| 103.144.87.192 | Viet Storage | 65495/33280 (both MSS 65495) | 741 | Two Nuclei window variants |
| 179.43.146.42 | Private Layer | 32120 / 65495 | 153 | Custom scanner + Nuclei |
| 193.32.127.220 | 31173 Services | 65495 / 65535 (MSS 1284) | 21 | Nuclei + deep proxy tool |
| 220.202.152.103 | China Unicom | 65495 / 64240 (MSS 1360) | 4 | Nuclei + tunnel tool |
| 72.60.104.48 | Hostinger | 65495 / 64240 (MSS 1460) | 2 | Nuclei + standard Linux |
The pattern of Nuclei window variants (65495 + 33280) appearing together on the same IP is consistent across the top three scanners (OVH, Ghosty, Viet Storage). This likely reflects different Nuclei execution contexts or configuration variants rather than distinct tools.
Private Layer’s 179.43.146.42 continues to be the only IP pairing the unique window 32120 custom scanner with Nuclei, maintaining its distinctive multi-tool profile from previous weeks.
Censys JA4T Comparison (Host vs. OAST Session)
| IP | Censys JA4T (host) | OAST JA4T (scanner) | Match? | Interpretation |
|---|---|---|---|---|
| 179.43.146.42 | 31856_2-4-8-1-3_1460_7 |
32120_2-4-8-1-3_1460_7 |
No | Custom TCP stack on scanner (window 32120 vs 31856) |
| 216.105.164.20 | 42340_2-1-1-4-1-3_1460_7 |
42340_2-1-1-4-1-3_1460_7 |
Yes | VPN node, scanner runs through it |
| 46.151.182.62 | 65504_2-4-8-1-3_1436_7 |
65495_2-4-8-1-3_65495_7 |
No | Host=standard, scanner=Nuclei loopback |
| 80.87.206.76 | 65160_2-4-8-1-3_1460_7 |
65495_2-4-8-1-3_65495_7 |
No | Host=standard, scanner=Nuclei loopback |
| 125.133.193.135 | 65535_2-1-3-4-8_1460_8 |
64240_2-4-8-1-3_1460_10 |
No | Both non-standard but different; VPN artifact on both |
| 45.61.131.28 | No services visible | 64240_2-4-8-1-3_1460_7 |
N/A | No Censys baseline (bulletproof, zero ports) |
The Censys-vs-OAST comparison is particularly useful for 179.43.146.42 (Private Layer): Censys sees the host’s native window (31856), while OAST sessions show 32120 – confirming the scanning tool modifies the TCP window at the application level.
Threat Intelligence Enrichment
External intelligence from VirusTotal, Censys, and Feedly Threat Graph was layered onto eight priority IPs. Full enrichment details are in threat-intelligence-enrichment.md.
Key enrichment findings:
- Two Censys-confirmed bulletproof hosting providers: Private Layer (179.43.146.42) and RouterHosting/Cloudzy/FranTech (45.61.131.28), both labeled BULLETPROOF with 0.75 confidence
- Russian attribution through French hosting: 80.87.206.76 registered to Alliance LLC, Moscow via OVH; forward DNS
ir6k1.2monkeyd.online; Gmail abuse contact - Commercial VPN identification: 216.105.164.20 confirmed as AnchorFree/Hotspot Shield VPN exit node via Hydra Authentication certificate chain
- Compromised gaming server indicator: 46.151.182.62 runs Valve/Source Engine protocol alongside scanning tools
- Expanding CVE toolkit on bulletproof infrastructure: 179.43.146.42 added CVE-2026-0770 (Langflow RCE) to its exploitation portfolio this week
CVE Intelligence (Feedly Threat Graph):
| CVE | Product | CVSS | PoC | Patch | Threat Actors | OAST IPs |
|---|---|---|---|---|---|---|
| CVE-2026-1731 | BeyondTrust RS/PRA | 9.8 | Yes (GitHub) | Yes (BT26-02) | HAFNIUM | 125.133.193.135, 179.43.146.42 |
| CVE-2026-0770 | Langflow | 9.8 | Yes (GitHub) | No | – | 179.43.146.42 |
| CVE-2026-23760 | SmarterMail | 9.3 | Yes (Telegram) | Yes (Build 9511) | – | 125.133.193.135 |
CVE-2026-1731 (BeyondTrust) is associated with HAFNIUM and linked to Lumma Stealer, SparkRAT, and VShell malware deployments. CVE-2026-0770 (Langflow) has no vendor patch and targets AI/LLM orchestration infrastructure. CVE-2026-23760 (SmarterMail) exploits were shared on underground Telegram channels within days of disclosure, with confirmed ransomware campaign usage.
Attribution Assessment
Confidence: Medium
This week’s single-IP campaign structure simplifies per-IP attribution but makes cross-campaign coordination harder to establish.
What we know:
- Every campaign maps to exactly one IP – no shared infrastructure across campaigns this week
- Six IPs run multiple campaigns (sequential tool runs, not coordinated operations)
- The
*jgo7campaign pattern (OVH/Alliance LLC) indicates automated sequential execution - Private Layer 179.43.146.42 maintains the unique window 32120 fingerprint from previous weeks, confirming operational continuity
- 45.61.130.7 and 45.61.131.28 share the same /22 network (RouterHosting) but run different campaigns
What we infer:
- The single-IP pattern may reflect a shift away from distributed scanning operations, or simply different operators this week
- The AnchorFree VPN exit node (216.105.164.20) conceals the true origin of the scanner behind it
- Alliance LLC Moscow registering through OVH France represents deliberate jurisdictional arbitrage
- The Ghosty Networks gaming server (UDP 27015) may be compromised rather than purpose-built scanning infrastructure
Network IOCs
Primary IPs (by session count):
| IP | ASN | Country | Sessions | Priority |
|---|---|---|---|---|
| 80.87.206.76 | AS16276 (OVH/Alliance LLC Moscow) | FR | 941 | HIGH |
| 46.151.182.62 | AS205759 (Ghosty Networks) | LU | 746 | HIGH |
| 103.144.87.192 | AS135932 (Viet Storage) | VN | 741 | HIGH |
| 45.61.131.28 | AS14956 (RouterHosting/Cloudzy) | US | 350 | HIGH |
| 125.133.193.135 | AS4766 (Korea Telecom) | KR | 333 | MEDIUM |
| 207.148.20.225 | AS20473 (Vultr) | US | 317 | MEDIUM |
| 216.105.164.20 | AS9009 (M247/AnchorFree VPN) | US | 293 | LOW |
| 179.43.146.42 | AS51852 (Private Layer) | CH | 175 | CRITICAL |
OAST Domains/Provider:
- All 33 campaigns use Interactsh
- 5,560 unique callback domains observed
- Domains distributed across
oast.pro,oast.live,oast.fun,oast.me,oast.sitevariants
JA4T Fingerprints for Detection:
32120_2-4-8-1-3_1460_7– Private Layer unique window (single-actor tracking)42340_2-1-1-4-1-3_1460_7– AnchorFree VPN infrastructure65495_2-4-8-1-3_65495_7– Nuclei/loopback primary (broadest coverage: 12 IPs)33280_2-4-8-1-3_65495_7– Nuclei variant (3 IPs)65535_2-1-3-1-1-8-4-0_1284_6– Deep proxy chain (new fingerprint)64240_2-4-8-1-3_1460_10– Unusual TTL 10 (Korea Telecom)
Domain/Certificate IOCs:
aliyundunupdate.xyz(typosquat of Alibaba Cloud security)dns.nullsproxy.com(Private Layer cert)ir6k1.2monkeyd.online(Alliance LLC Moscow forward DNS)mchcz.com(RouterHosting historical resolution)- AnchorFree Hydra Authentication RSA SubCA (commercial VPN indicator)
- Proxmox VE cert with misspelled “promox.d” (Korea Telecom)
JARM Hashes:
2ad2ad0002ad2ad00042d42d0000005d86ccb1a0567e012264097a0315d7a7– Private Layer2ad2ad0002ad2ad0002ad2ad2ad2ada14bf7dda7990c918ac83e6dc5fe2b8f– AnchorFree VPN
Detection Recommendations
Block 179.43.146.42 (Private Layer bulletproof) and associated domain
aliyundunupdate.xyz. This IP maintains active C2 infrastructure with expanding CVE exploitation including unpatched Langflow RCE.Block 45.61.131.28 and 45.61.130.7 (RouterHosting/Cloudzy/FranTech). Censys-confirmed bulletproof hosting with Cloudzy abuse contact. Zero exposed services = purpose-built scanning infrastructure.
Block or alert on 80.87.206.76 (Alliance LLC Moscow via OVH). Russian-registered entity with 3-year scanning history and ProxyLogon focus.
Monitor the JA4T fingerprint
32120_2-4-8-1-3_1460_7across all sensors. This unique TCP window tracks a single actor across the Private Layer IP and now also 109.236.50.39 (LeaseWeb Netherlands) – potential infrastructure expansion.Alert on
aliyundunupdate.xyz:8084/sltas an active C2 endpoint, and179.43.146.42/xas a potential payload download URL.Prioritize patching for CVE-2026-0770 (Langflow) – no vendor patch available, public PoC since Feb 8, confirmed exploitation in the wild.
Consider VPN exit node policies for 216.105.164.20 (AnchorFree/Hotspot Shield). This is commercial VPN infrastructure, not dedicated attack infra, but scanners actively use it for anonymization.
Alert on MCP and SSE endpoint scanning (7 occurrences, 3 IPs) – emerging attack surface targeting AI/LLM infrastructure.
GNQL Queries
tags:"Contains Well-known Out-of-band Interaction Domain" last_seen:7dmetadata.asn:AS51852 last_seen:7d classification:maliciousmetadata.asn:AS14956 last_seen:7d classification:maliciouscve:CVE-2026-0770 last_seen:7dcve:CVE-2026-1731 last_seen:30dip:179.43.146.42 OR ip:45.61.131.28 OR ip:80.87.206.76 OR ip:46.151.182.62Week-over-Week Comparison
| Metric | Feb 7-13 | Feb 14-20 | Change |
|---|---|---|---|
| Sessions | 6,197 | 3,882 | -37.4% |
| Unique IPs | 79 | 24 | -69.6% |
| OAST Domains | 7,691 | 5,560 | -27.7% |
| Campaigns | 73 | 33 | -54.8% |
| Decode Rate | 100% | 100% | – |
| Nuclei Sessions | 1,276 | 2,547 | +99.6% |
| Bulletproof IPs | 2 | 2 | – |
Session volume declined by 37.4% and unique IPs by 69.6%, but Nuclei-based scanning nearly doubled. The concentration into fewer, higher-volume single-IP operations contrasts with the previous week’s distributed multi-IP campaigns. The Cloudflare-proxied cluster that dominated last week (2,973 sessions) is absent this week, accounting for the bulk of the IP count decline.
Continuing actors: Private Layer (179.43.146.42), Viet Storage (103.144.87.192), AS215540 (now 185.138.89.4 replacing 46.29.235.157).
No longer observed: PROSPERO OOO (193.24.123.42), Oracle Cloud Brazil (204.216.147.144), Cloudflare proxy cluster.
New actors: Ghosty Networks (46.151.182.62), RouterHosting/Cloudzy (45.61.131.28), AnchorFree VPN (216.105.164.20), Alliance LLC Moscow via OVH (80.87.206.76).